Unlocking the Potential of Aneka Cloud: A Gateway to Modern Cloud Computing
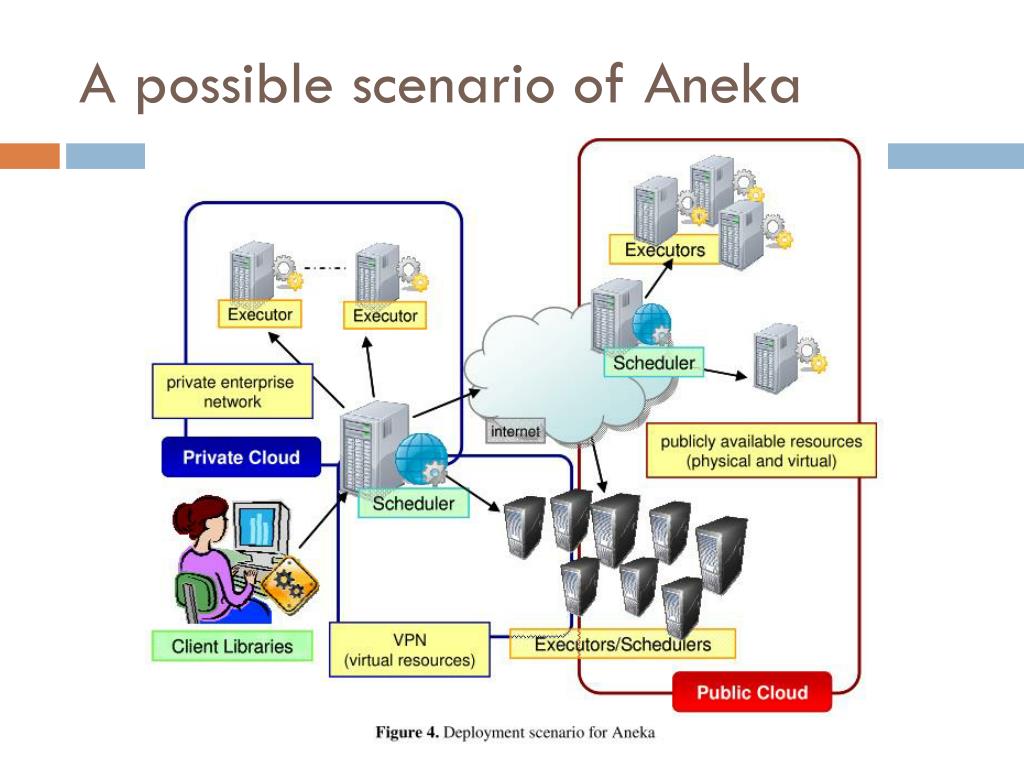
The Power of Aneka Cloud: Revolutionizing Cloud Computing In the fast-paced world of technology, cloud computing has emerged as a game-changer, offering businesses and individuals a flexible and scalable way to store, manage, and process data. Among the myriad of cloud computing platforms available today, Aneka Cloud stands out as a powerful and innovative solution […]
Read More →