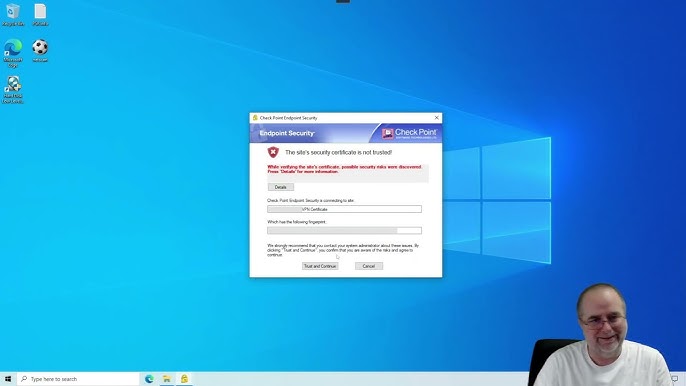
Enhancing Security with Check Point Remote Access VPN Solutions
The Importance of Check Point Remote Access VPN Remote access Virtual Private Network (VPN) solutions have become increasingly vital in today’s digital age, especially with the rise of remote work and the need for secure connections outside traditional office environments. One prominent player in this field is Check Point, a leading cybersecurity company known for […]
Read More →